TOPICAL ISSUES ON PROVIDING BIOMETRIC SYSTEM SECURITY
Серикова Ю.И.1, Князев В.Н.2
1 ORCID: 0000-0002-4959-321X, магистрант, Пензенский государственный университет; 2 кандидат технических наук, доцент, Пензенский государственный университет
АКТУАЛЬНЫЕ ПРОБЛЕМЫ БЕЗОПАСНОСТИ БИОМЕТРИЧЕСКИХ СИСТЕМ АУТЕНТИФИКАЦИИ
Аннотация
В статье поднимаюся вопросы высоконадежной аутентификации пользователей информационных систем. Особое внимание уделяется актуальным проблемам безопасности биометрических систем аутентификации и излагается авторский подход к повышению надежности таких систем. Рассматриваются биометрические технологии, которые можно использовать для сохранности информационных ресурсов (защищенности законных прав владельцев ресурсов), их преимущества и недостатки.
Ключевые слова: биометрические средства защиты информации, биометрический образ, аутентификация, уязвимости систем контроля и управления доступом, шифр Вермана.
Serikova Y.I.1, Knyazev V.N.2
1ORCID: 0000-0002-4959-321X, Postgraduate student, PenzaStateUniversity; 2 PhD in Engineering, associate professor, Penza State University
TOPICAL ISSUES ON PROVIDING BIOMETRIC SYSTEM SECURITY
Abstract
The article deals with the problems of safe and highly reliable recognizing the identity of Information Management System (IMS) users. It gives particular attention to the topical problems of biometric system security and dwells upon the author’s approach to the problem of enhancing security in biometrics-based authentication systems. The article also touches upon the biometric technologies that can be used to provide information security, as well as their advantages and disadvantages.
Keywords: biometric information security features, biometric parameters, identification (authentication), weak points of the access control system, one-time pad (Vermann Cipher).
The need to protect information systems is increasing. It is conditioned by the rise in the cost of information, its importance as well as a rapid development of information technologies. Information is referred to as both exposed and protected by the state data on the military, foreign-policy, economic, intelligence, reconnaissance, investigation and other activities of the country, unauthorized spread of which can damage national security [1].
Today one of the most important tasks to enhance information systems is to intensify the development of methods and means of data access control. Identification or authentication is one of the main functions to control data access. Biometric characteristics possess such properties as reliability, authenticity and usability.
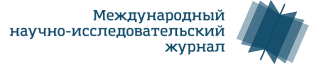
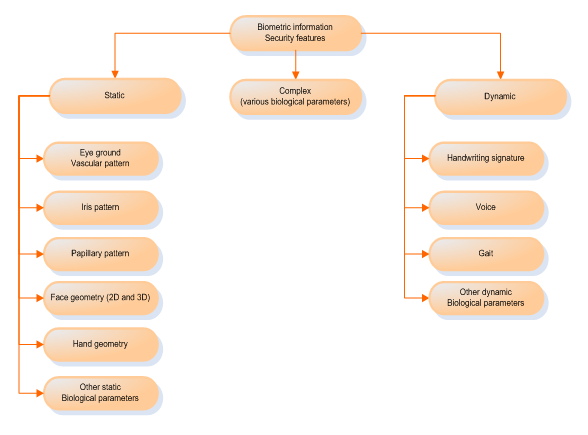
Biometric technologies are developed for security applications in the systems of different civil and military facilities in all developed countries [2]. Biometric information security techniques are divided into three main groups: static, dynamic and complex (multimodal) (Fig.1). Static methods are based on analyzing a unique physiological parameter, dynamic ones - a behavioral feature and the latter include various biological characteristics. Biometric technologies have become an essential component of both national and international IT-market. The biometric technology most widely used today is papillary pattern recognition (43.6%). Then there is face recognition – 19%, interim biometric technologies – 11.40%, hand recognition – 8.8%, iris recognition – 7.10%, voice analysis and multi biometric technologies – 4%, handwriting signature – 1.70% (Fig.2).
Fig.1 – Biometric information security features
Fig.2 – Market distribution of biometric technologies
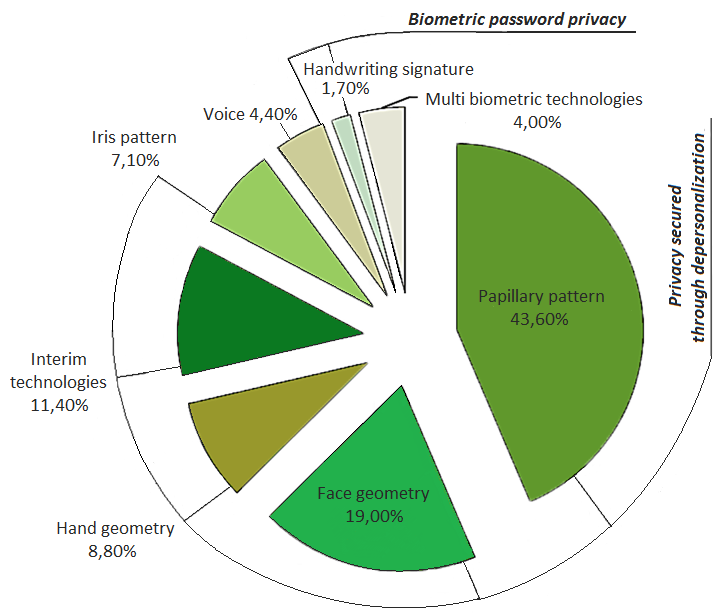
There is a definite opinion on biometric technologies today. Among the advantages of static methods is a relative simplicity of identification (Users don’t need to make any special efforts or to have certain psychological condition to measure static parameters.). But it should be noted that static methods are characterized by such essential drawbacks as invariability and exposure of human static biometric parameters (there is a possibility of identifier forgery), high cost of current biometric technologies and a high probability of False Acceptance Rate (FAR) at a 10-7 – 10-12 level [3] (physical limits of the uniqueness of personal static parameters prevent image element recognition from being more accurate).
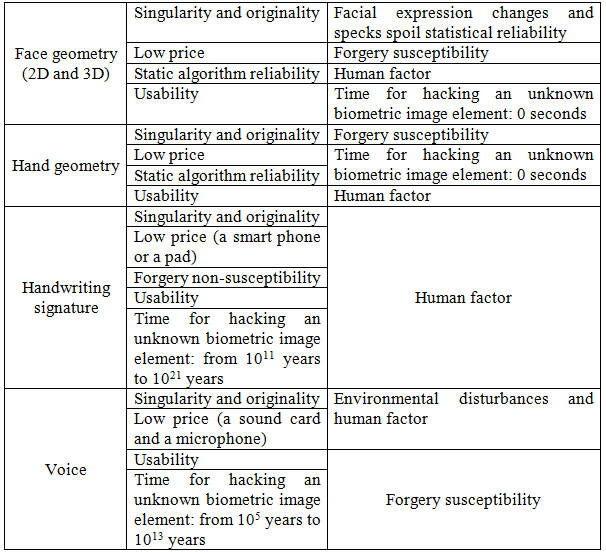
These drawbacks can be eliminated through the use of dynamic methods, which make it possible to change a scanned image element. It is should be noted that dynamic methods are not very expensive to implement and enable (for some systems) biometric image elements to be depersonalized. However, the most serious drawback of dynamic methods is human mental and physiological instability. The advantages and disadvantages of the major biometric technologies are presented in table 1.
Table 1 – The advantages and disadvantages of the major biometric technologies
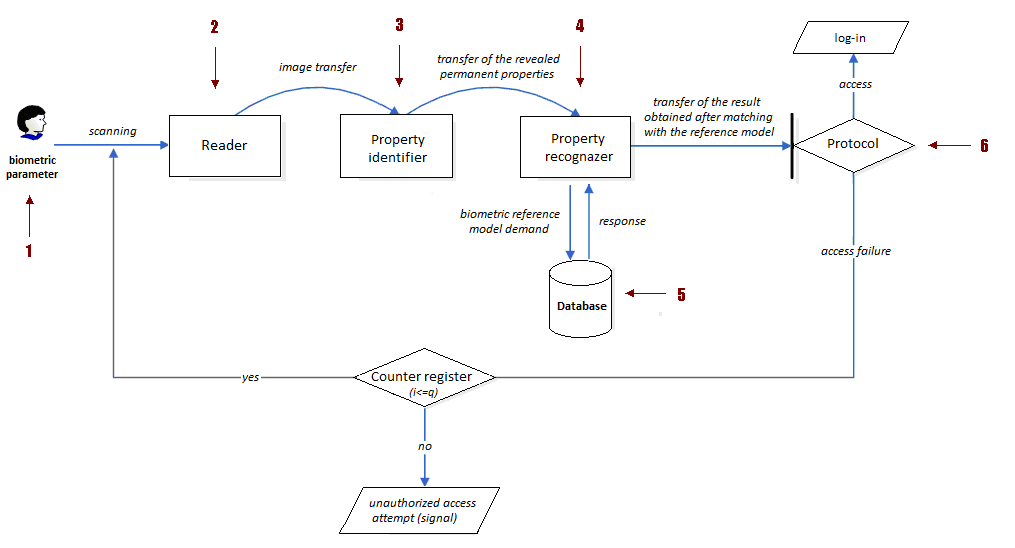
According to research data [4] highly-reliable biometric technologies put together in table 1 are presented by the two last technologies based on handwriting recognition and voice analysis. Biometric parameters are unique identifiers, but the problems of their secure storage and protection from forgery and interception are still unsolved. Hacking can take place if to use the weak points of the biometric system. Biometric recognition system functionality is presented in figure 3[5]. All the weak points of the access control system are marked with numerals.
Fig.3 – Weak points of the access control system
The following types of biometric system weak point attacks are currently revealed:
- Biometric image attack;
- Attacks through the retransmission of real-world information (interception);
- Reference model database manipulation;
- Attacks through reverse engineering.
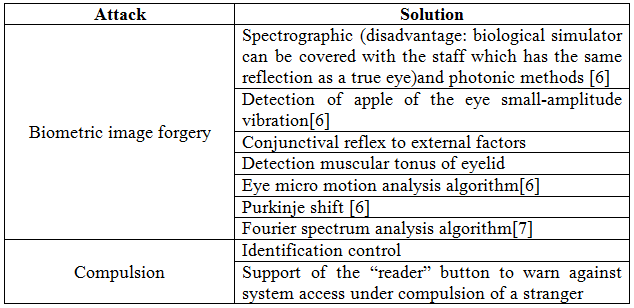
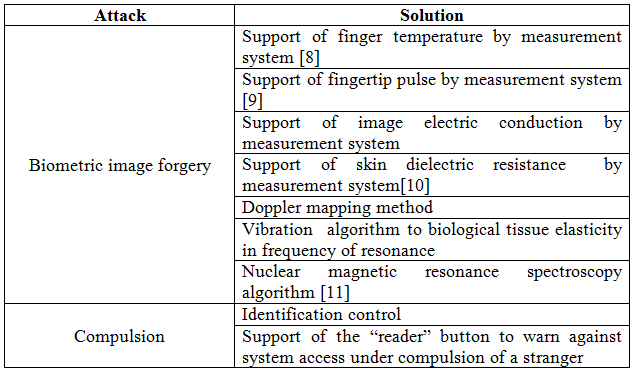
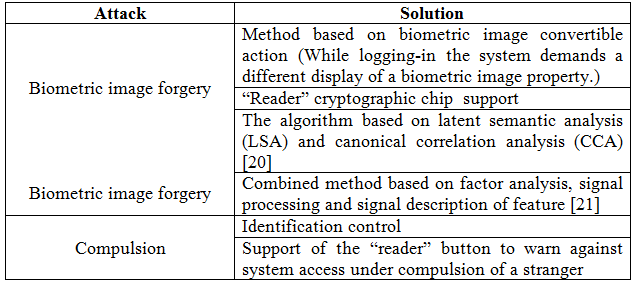
Tables 2 – 6 describe some biometric technologies to attack the biometric image elements and contain the information on the ways of attack repelling.
Table 2 – Biometric iris recognition system
Table 3 – Biometric papillary pattern recognition system(AFIS)
Table 4 – Biometric face geometry (2D and 3D) recognition system
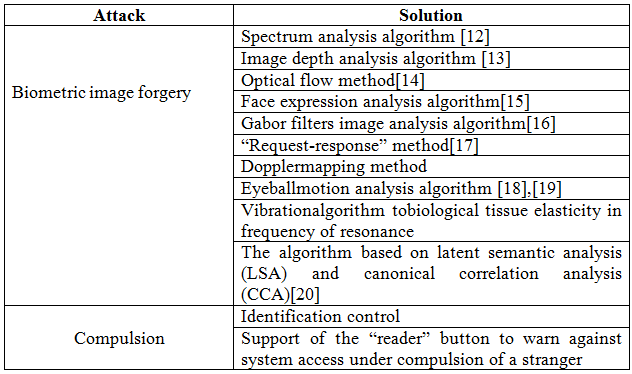
Table 5 – Biometric voice analysis system
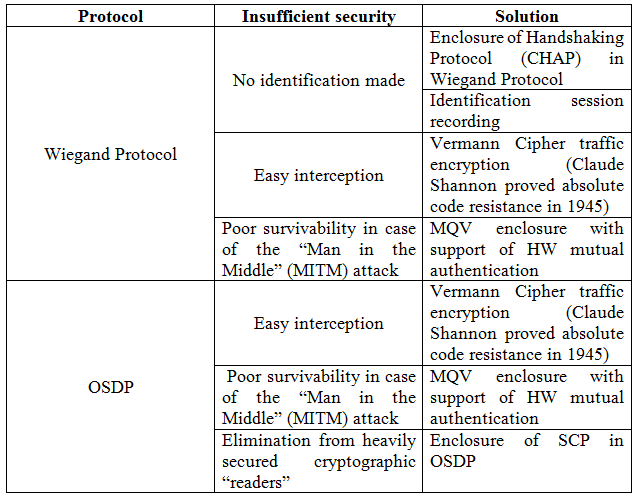
Present-day “readers” utilize Wiegand Protocol and Open Supervised Device Protocol (OSDP). They both meet the requirements of State Standard Specification ISO/IEC 24713-1-2013 [22]. It should be noted that these protocols have some drawbacks (Table 8).
Analyzing the IMS safety risks, one needs to pay attention to such an important aspect as database operational protection. How should one prevent a malicious hacker from gaining access to a person’s biometric data? It is a difficult problem to solve. Trying to do it one should deal with each database management system (Oracle, MySQL, Sybase, etc.) separately.
Table 6 – The advantages and disadvantages of Wiegand Protocol and Open Supervised Device Protocol (OSDP)
Before enhancing database security, one should give consideration to the security of database information.
There are two methods to protect database biometric reference models:
- Transformation of biometric parameters and their cryptographic protection;
- Storage of certain properties rather than a biometric image itself (e.g. neuronet weight factors storage solely).
The proposed solutions thereby help to enhance the biometric system efficiency and security.
Conclusion
Information technologies are being widely used in today’s IT world. The problem of information security is thus becoming topical. New methods to protect information systems are developed every year. They help to improve the system safety and resistance. One of the ways to provide information security is identification (authentication).
The most rapidly developed information security methods are biometric ones. In spite of the fact that foreign systems more often use papillary pattern recognition, it has been found experimentally that this method cannot be used in high-level military identification systems in the field in different weather conditions [23].
We have analyzed current and prospective biometric technologies and can make the following conclusion: handwriting signature is the safest and most reliable biometric technology. The time for hacking a biometric image element of this kind is from 1011 to 1021 years [3,4]. Future urgently needed researches will concentrate on developing safe and highly reliable smart techniques using the solutions proposed in this article.
References
- Serikova, Y.I. Information security in modern IMS / Y.I. Serikova, I.Y. Balashova, D.V. Taktashkin // VI Proceedings of the international scientific-technical conference – Penza: High Professional Education MSUTM them. K.G. Razumovsky – 2015– P.158-160.
- Knyazev, V.N. Improving the reliability of the authentication system by compensating for systematic error normal deviation, computational on small samples biometric parameters/ V.N. Knyazev, Y.I. Serikova // III Proceedings of the international competition – Lipetsk: Scientific partnership «Argument» – 2016 – P.55-60.
- Akhmetov, B.S., Volchihin, V.I., Ivanov, A.I., Kartbayev, T.S., Malygin, A.Y. Highly reliable multi-biometric authentication of human-being personality to support citizens interaction with E-government and E-business // III World conference on information technology. 14-16 November, 2012, University of Barcelona, Faculty of Library and Information Science, Barcelona, Spain. P. 74 – 81.
- Serikov, I.V. Status and prospects of development of biometric authentication technologies / I.V.Serikov, Y.I.Nikitchenko, A.A.Vakhromeev // Reliability and quality: Proceedings of the International Symposium. – 2010. – Volume 2. - P. 226-228.
- Knyazev, V.N. Research significance multidimensional sampling in evaluating the biometric / V.N. Knyazev, Y.I. Serikova // Questions electronics. Series "display special equipment and control systems" (SOIU), 2015. - Issue 2 – P. 114-123.
- Daugman, J.G. Iris Recognition and Anti-spoofing Countermeasures // VII International Biometrics Conference, London, 2004.
- Daugman, J.G. High confidence personal identification by rapid video analysis of iris texture // Proc. Of the IEEE, International Carnahan conference on security technology–1992–P.50-60.
- Osten, D.W., Carim, H.M.,Areson, M.R., Blan, B.L. Biometric. Personal authentication system. Minnesota mining and Manufacturing Company: Patent US #5,719,950, Febrary’17, 1998.
- Lapsley, P.D., Less, J.A., Pare, D.Jr., Hoffman, N.// Anti-Fraud biometric sensor that accurately detects blood flow, Smart Touch, LLC: Patent US #5,737,439, April’7, 1998.
- Kallo,P., Kiss, I., Podmaniczky, A., and Talosi, J.: Detector for recognizing the living character of a finger in a fingerprint recognizing apparatus, Dermo Corporation, Ltd. U.S. Patent #6,175,64, January’16, 2001.
- Nixon, K. A., Rowe, R. K., Allen, J., Corcoran S. et al. Novel spectroscopy-based technology for biometric and liveness verification//Proc. Biometric technology for human identification, 2004. V. 5404. P. 287-295.
- Wang, Y., Tan, T., Jain, A. K. Live Face Detection Based on the Analysis of Fourier Spectra//Proc. SPIE. V. 5404, Biometric Technology for Human Identification. 2004. P. 296 — 303.
- Choudhury,T., Clarkson, B., Jebara, T., Pentland, A. Multimodal person recognition using unconstrained audio and video//International Conference on AVBPA, 1999. P. 22-28.
- Aggarwal, J. K., Nandhakumar, N. On the Computation of Motion from Sequences of Images — A Review//Proc. IEEE, 1998. V. 76. P. 917-935.
- Bigun, J., Fronthaler, H., Kollreide, K. Assuring liveness in biometric identity authentication by real-time face tracking, CIHSPS2004//IEEE International Conference on Computational Intelligence for Homeland Security and Persona] Safety, Venice, Italy, 21-22 July. P. 104-112. IEEE Catalog No. 04EX815, 2004.
- Speakers, K.A., Spitcin, V.G., Hamker, F. Finding settings and delete the constant component of the Gabor filter for image processing/ K.A. Speakers, V. G. Spitcin, F. Hamker // Proceedings of TPU. - Tomsk: TPU, 2011. - T. 318, №5: Management. Computer Science and Informatics. - P. 57-59
- Access the protected resource:: http://www.identix.com/
- Hyung-KeunJee, Sung-Uk Jung, Jang-HeeYoo. Liveness Detection for Embedded Face Recognition System//Proceedings of World Academy of Science, Engineering and Technology, 2006. 18. P. 29-32.
- Deng, G., Coo, B., Miao, J., Gao, W., Zhao, D. A Liveness Check Algorithm Based on Eye Movement Model Using SVM// The Chinese Journal of Computer aided design and computer graphics (in Chinese language). 2003. V. 15. №7. P. 853-857.
- Chetty, C., Wagner, M. Liveness detection using cross modal correlations in face-voice person authentication// INTERSPEECH-2005. 2005. P. 2181-2184
- Access the protected resource: http://www.dslib.net/zaw-informacia/metodika-i-kompleks-sredstv-ocenki-jeffektivnosti-autentifikacii-golosovymi.html
- Requirements of State Standard Specification ISO/IEC 24713-1-2013 «IT. Biometric profiles to interact and exchange data. Part 1. The overall architecture of a biometric system and biometric profiles».
- Serikova, N.I.,Malygin, A.Y., Volchihin, V.I., Oleynik, Y.I. «Biometrics -11-P»: A final report on the research work – Penza: High Professional Education PSU – 2012– P.1- 64.