МЕТОДОЛОГИЯ ПОСТРОЕНИЯ МОДЕЛИ РЕАЛИЗАЦИИ ИНФОРМАЦИОННЫХ УГРОЗ ЭКОНОМИЧЕСКОЙ БЕЗОПАСНОСТИ
Глотина И.М.
Кандидат экономических наук, доцент
ФГБОУ ВО Пермская ГСХА
МЕТОДОЛОГИЯ ПОСТРОЕНИЯ МОДЕЛИ РЕАЛИЗАЦИИ ИНФОРМАЦИОННЫХ УГРОЗ ЭКОНОМИЧЕСКОЙ БЕЗОПАСНОСТИ
Аннотация
В статье предложена методология построения модели реализации информационных угроз экономической безопасности государства. Сформулированы основные термины элементов моделирования. Разработанная информационная модель учитывает виды источников угроз; факторы (уязвимости), способствующие их реализации; последствия реализации угроз; объекты безопасности; субъекты обеспечения безопасности и служит основой для разработки системы обеспечения экономической безопасности государства.
Ключевые слова: моделирование, источник угроз, факторы, уязвимости, угрозы, последствия.
Glotina I.M.
PhD in Economics, Associate Professor,
Perm State Agricultural Academy
METHODOLOGY CONSTRUCTION OF INFORMATION THREATS IMPLEMENTATION MODEL OF ECONOMIC SECURITY
Abstract
The paper proposes methodology construction of information threats implementation model of the state economic security. Basic terms of modeling components have been formulated. The developed information model includes types of information threats; vulnerability factors that contribute to their implementation; threat consequences; security objects; security control subjects and forms the basis for ensuring system development of the state economic security.
Keywords: modeling, threat source, vulnerability factors, threats, consequences.
In the modern conditions, the necessity to provide economic security of a state is caused by a high probability level and scale of economic and moral losses, which reasons are directly related to information. The fundamental of efficient security supply for any object is the creation of a true security threat model containing threats that are ranked upon criteria and their sources, as well as potential consequences of threat implementations – harm, damage.
Modeling is the basic element of the system approach to learning processes of nature, society, technical systems, and their management. In general, a security threat model is an informational model including complex of elements that describes object safety condition in the case of occurrence of particular dangerous events and processes, as well as object’s relationships with the outside world [1]. Modeling issues are handled in studies of following authors V.I. Koroleva, A.A. Novikova, A.S. Businova, G.P. Zhigulina, A.S. Shaburova, S.P. Rastorgueva, D.A. Gubanova, D.A. Novikova and others [2-5].
Unfortunately, there is no coherent and complete methodology of the creation of economic security information threat model in the modern world. The author of the article has attempted to organize basic techniques and definitions in order to form a unified methodological approach for such model creation.
The modeling considers the following logical sequence of its elements interplay:

Figure 1 - Logical sequence of modeling elements
The model is formed in descriptive manner as a result of conclusions and classified as a verbal informational model.
The following terminology is used in the process of modeling.
Threat sources – actual or potential carriers of information threats. The range of information threats sources is divided into 3 main groups, such as natural, technogenic, and anthropogenic.
Objective and absolute circumstances of force majeure are represented by natural sources. These include natural disasters or any other circumstances which cannot be avoided at current level of human knowledge and abilities: fire, earthquakes, floods, hurricanes, unforeseen events, supernatural phenomena or other extraordinary circumstances. As a rule, these circumstances are external towards protected objects.
Sources, determined by level of civilization development, technocratic human activity, form a group of technogenic sources. Activity of these sources is weakly predicted, strongly depends on equipment properties and its operating conditions, and therefore requires special attention.
Technical means as a potential source of information threats can be divided into external and internal. The first group is represented by means of telecommunication and information exchange, communication lines; the second by equipment support and software of information processing; security and safety means, such as alarm system, telephony or other technical means applied in practice.
Subjects, deliberate or accidental acts which could cause damage are regarded as anthropogenic sources. In terms of ensuring protection, this kind of acts may be determined, predicted and prevented. Examples of anthropogenic threat sources include subjects who have authorized or unauthorized access to work with organic assets of protected objects and whose actions might compromise information security.
A distinction is made between internal and external anthropogenic sources. Examples of external sources include criminal structures; hackers; unfair partners; operating staff of telecommunication service suppliers; managers of supervisory authorities and emergency services; security agents. External sources most frequently appear due to interstate cooperation in military sector, politics and economic sphere.
Internal sources are represented by qualified specialists in development and exploitation of technical means and software with knowledge of specific challenges, structure and main operating principles of information protection firmware, who is allowed to use standard equipment and technical means. Special category within external and internal anthropogenic sources is constituted by persons with mental impairment, related infiltration and recruited agents. Threat countering and prevention for this group has its own specificity.
Threat sources exploit vulnerabilities to breach information security, gain illegal profit, compromise owner or user of information. Vulnerability factors present security object reasons that lead to information security breach on a particular object and appear due to operation process flaws, features of automation system architecture, exchange protocols and interfaces, applicable software and hardware, operating conditions, insufficient knowledge level of information resources users.
Vulnerabilities are divided into objective, subjective and accidental. Objective vulnerabilities depend on design and technical specifications of equipment used at protected object. Total elimination of vulnerabilities is not possible, but they might be significantly declined with engineering technical methods of information security counter threats.
Subjective vulnerabilities depend on actions of informational resources owners and staff. Organizational, legal and hardware-software methods are used to eliminate such kind of vulnerabilities.
Accidental vulnerabilities depend on environmental features at the territory of protected object. As a rule, they are weakly predicted and can be eliminated through the complex of organizational and engineering measures of information threat countering.
Vulnerabilities elimination and decline has a profound impact on information security threat.
The RF Federal Law On safety interprets term “Threat” as “a complex of conditions and factors that cause danger for vital interests of government, person and society” [6]. Threats, as potential dangers of any actions against protected object, do not occur in themselves but through vulnerabilities, causing threat realization.
The following illegal activities are recognized as threat implementation methods:
- information theft (copying);
- information destroying;
- information modification (distortion);
- breach of information accessibility (blocking);
- breach of information confidentiality;
- denial of information authenticity;
- imposing of false information.
Threat realization leads to the following consequences:
- material, moral, physical damage due to disclosure of personal information;
- material and reputational damage caused by disclosure of confidential information;
- material and reputational damage due to restoring the violated informational resources;
- material and reputational damage due to failure to perform obligations against third party;
- material and reputational damage caused by disruption of economic agent operations;
- material, political and reputational damage due to failure in the management of international relations.
Damage can be caused by any subject as well as any consequence of natural disasters or technogenic impact.
The aim of modeling is to create a system of main threats that may cause damage or lead to the situation when damage is potentially possible. The article determines the following model elements: security objects, threat subjects, security control subjects.
The main security objects include:
- informational resources, containing state secret, commercial secret and any other confidential information;
- system of informational resources production, distribution and usage, which involves informational systems of various types and purposes, information technologies, collection rules and procedures, processing, storage and transfer of information, scientific, engineering and service staff;
- infrastructure of information, including information centers, information and telecommunication exchange gateways, maintenance of telecommunication nets and systems as well as information protection means and systems;
- citizens of the State as objects of information impact.
Safety of listed objects provides conditions for secure functioning of national institutions, legal entities and individuals.
Security threat subjects:
- individuals, social groups and communities, professional and informal structures, causing a threat (threat bearers);
- natural and technogenic phenomena and processes causing a threat (threat bearers).
Threat sources and security objects include any systems (social, natural, technical etc.) with specific complex of properties. The distinction between these two definitions lies in the fact that a security object has properties that are attractive for a threat source while a threat source has an ability to destroy (damage, remove, transform, capture, etc.) these properties.
Security control subjects – individuals, professional associations and government structures countering information threats (Fig. 2).
The range of considered security objects, potential threats and their implementation methods, determination of threat sources, methods and forms of their expression, possible consequences allow to lay the informational foundation for meeting the main challenges of ensuring security:
- forecast, detection, analysis and assessment of information threats;
- development and application of measure complex due to detection and prevention of information threats;
- determination, formation of organizational structure aimed to counter security threats; preparing of security control subjects to countering;
- coordination of security control subjects.
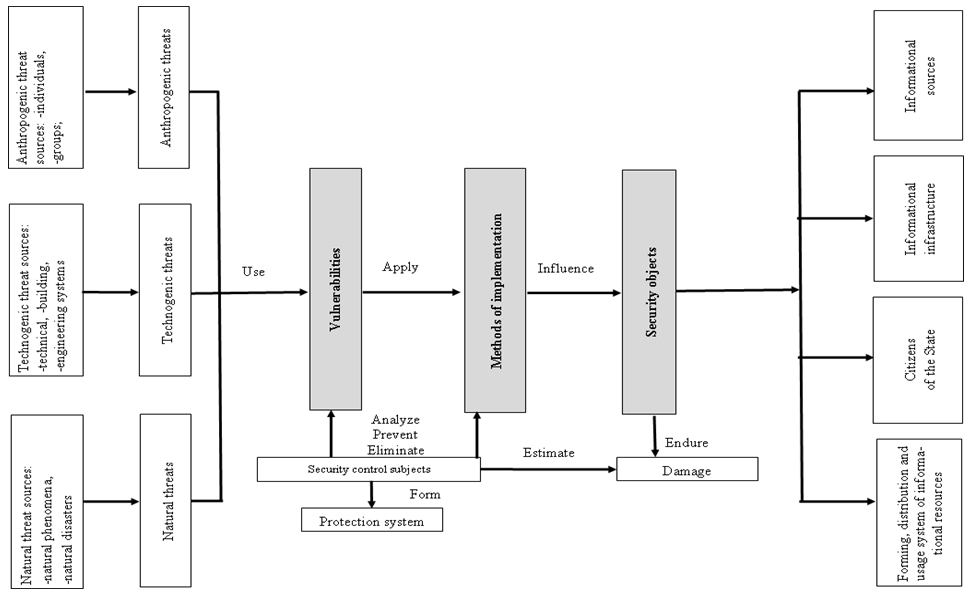
Figure 2 - Information threats implementation model
Due to dichotomy of information, in our opinion, a distinguish should be made between threats aimed to breach such information properties as integrity, accessibility, confidentiality and threats from information or information impact, aimed to change citizens’ attitudes, opinions, beliefs, behavior (Tab. 1).
Table 1 - Modeling of informational threat implementation
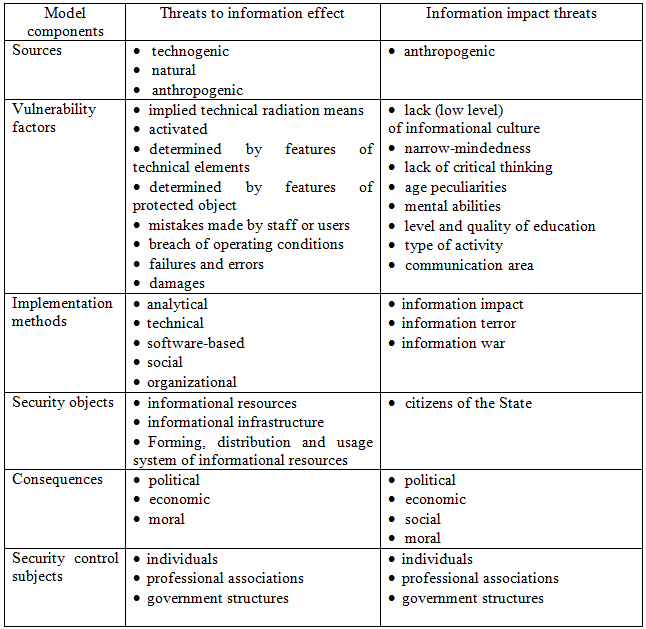
Professionals in the sphere of informational security deal with threats affecting information. Threat assessment methodologies base on risk analysis while security systems, as a rule, base on national and international guidelines and requirements from regulators. Assessment methodologies of information impact threats are absent. It is a field of research for psychology, philosophy, political science and economy.
Outlined approaches to the creation of information threat implementation model would improve the issues of information impact modeling and assessments of its impact to government economic security.
Список литературы / References
- Королев В.И., Новиков А.А., Кузьмин А.П., Шориков А.Н. Методология построения угроз безопасности территориально распределенных объектов // Интернет-журнал «Технологии техносферной безопасности». – 2013. - № 2(48) [Электронный ресурс]. – URL:http://ipb.mos.ru/ttb (дата обращения 22.03.2016)
- Бузинов А.С., Жигулин Г.П., Шабаев Р.И. Моделирование и прогнозирование информационных угроз как составная часть Концепции информационной безопасности РФ // Известия Российской академии ракетных и артиллерийских наук. – 2010. – № 4(66) [Электронный ресурс]. – URL: http://faculty.ifmo.ru/ikvo/MPES/downloads/modinfygr.doc (дата обращения: 15.07.2013).
- Шабуров А.С., Юшкова С.А., Бодерко А.В. Моделирование оценки угроз безопасности информационных систем персональных данных//Вестник ПНИПУ. Электротехника, информационные технологии, системы управления, - 2013.-№ 7, с. 149-159.
- Расторгуев С.П. Математические модели в информационном противоборстве. Экзистенциальная математика – М.: АНО ЦСОиП, 2014. – 260 с.
- Губанов, Д.А., Новиков Д.А., Чхартишвили А.Г. Модели информационного влияния и информационного управления в социальных сетях // Проблемы управления.- 2009. - №,. с. 28-35
- О безопасности: федеральный закон Российской Федерации от 28 декабря 2010 г. N 390-ФЗ // Рос. газ. – 2010. – 29 дек.
Список литературы на английском языке / References in English
- Korolev V.I., Novikov A.A., Kuzmin A.P., Shorikov A.N. Metodologiya postroeniya ugroz bezopasnosti territorialno raspredelennykh obektov [Security threats construction methodology for territorial distributed objects] [Electronic resource] // Internet-zhurnal Tekhnologii tekhnosfernoi bezopasnosti [Online magazine Technology of technogenic safety]. – 2013. – Vol. 48, №2. URL: http://ipb.mos.ru/ttb (accessed 22 March 2016). [in Russian].
- Buzinov A.S., Zhigulin G.P., Shabaev R.I. Modelirovanie i prognozirovanie informatsionnykh ugroz kak sostavnaya chast Kontseptsii informatsionnoi bezopasnosti RF [Modeling and Forecast of information threats as a part of RF information security concept] [Electronic resource] // Izvestiya Rossiiskoi akademii raketnykh i artilleriiskikh nauk [News of Russian Academy of Rocket and Artillery Science]. – 2010. – Vol. 66, №4. URL: http://faculty.ifmo.ru/ikvo/MPES/downloads/modinfygr.doc (accessed 15 July 2013). [in Russian]
- Shaburov A.S., Yushkova S.A., Boderko A.V. Modelirovanie otsenki ugroz bezopasnosti informatsionnykh sistem personalnykh dannykh [Security threat assessment modeling of personal data informational systems] // Vestnik PNIPU. Elektrotekhnika, informatsionnye tekhnologii, sistemy upravleniya [PNRPU Newsletter. Electrical engineering, information technologies and computer-aided systems]. – 2013. – №7, P. 149-159. [in Russian].
- Rastorguev S.P. Matematicheskie modeli v informatsionnom protivoborstve. Ekzistentsial'naya matematika [Mathematical models in informational confrontation. Existential maths]. – M.: ANO CSO&P, 2014. – 260 p. [in Russian].
- Gubanov D.A., Novikov, D.A., Chkhartishvili A.G. Modeli informatsionnogo vliyaniya i informatsionnogo upravleniya v sotsialnykh setyakh [Models of information impact and informational management in social nets] // Problemy upravleniya [Management issues]. – 2009. – №,. P. 28-35. [in Russian].
- O bezopasnosti: federal'nyi zakon Rossiiskoi Federatsii ot 28 dekabrya 2010 g. N 390-FZ [On Safety: Federal Act of the Russian Federation of 28 December 2010 N 390-FZ] // Ros. gaz. – 2010. – 29 Dec. [in Russian].